SSO/SAML Setup: OneLogin
Note: DataGrail only supports connections with SAML v2.0.
DataGrail OneLogin Application
- Create a DataGrail App in your OneLogin instance
- Integrate OneLogin with a read-only user. This will alert Legal when new applications are added/removed that may contain personal data so they can take appropriate action to comply with Privacy Regulations
Step 1: Build a SAML Test Connector (Advanced) App:
- Click the Administration Tab in the top right corner
- Select Users and then Custom User Fields.
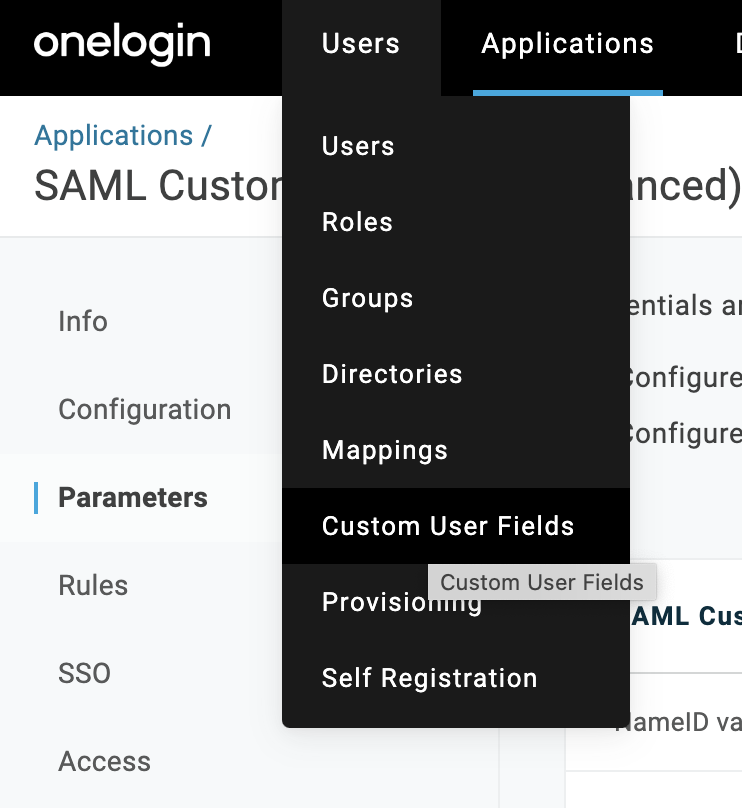
-
Add a new field called DataGrail Admin with
is_dg_adminfor the Shortname. -
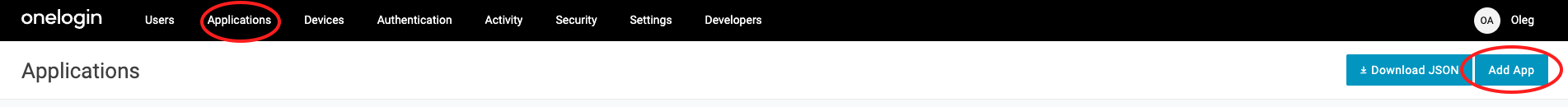
Go to Applicationsthen >> Add App
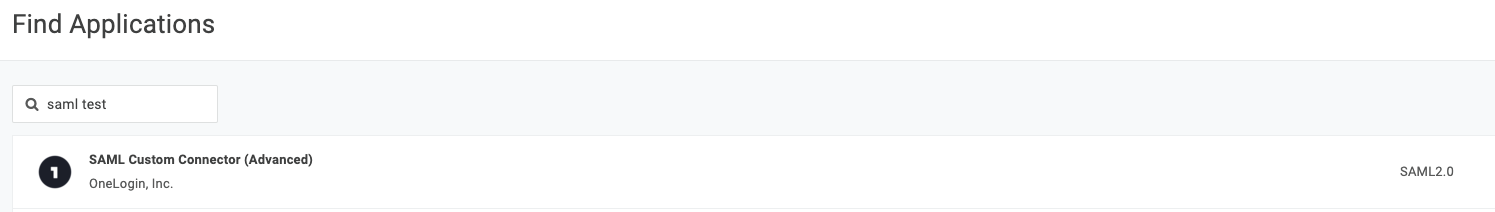
- Under Find Applications select SAML Custom Connector (Advanced)
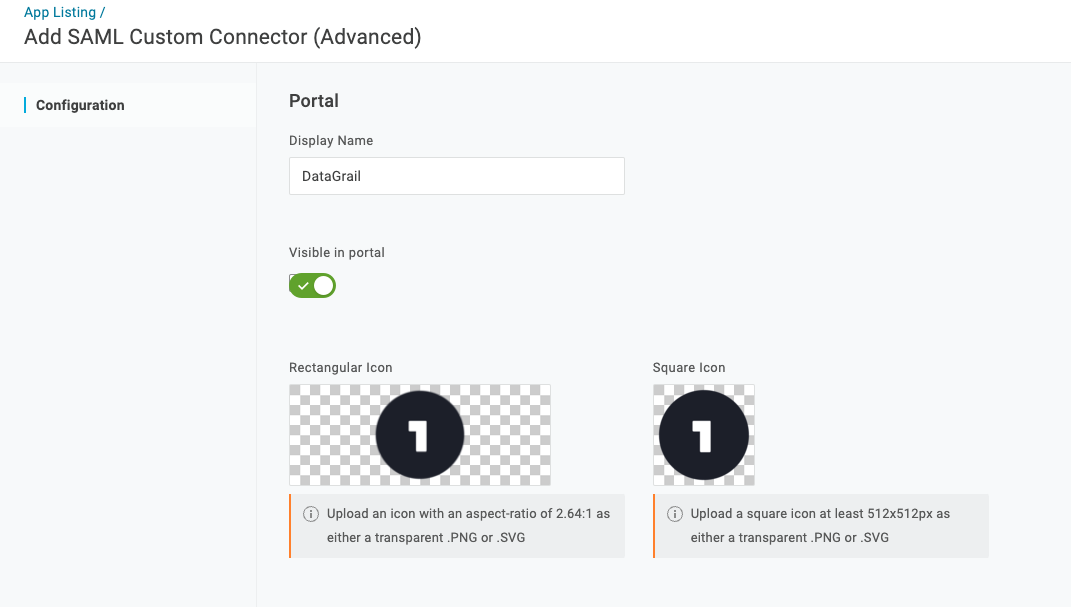
- Edit the Display Name to DataGrail and clickSave. Once complete, navigate to the Configuration tab on the left-hand menu.
-
Please edit the following fields in bold:
-
-
Audience (EntityID): https://[yourname].datagrail.io/saml/metadata
- Example: if TestCustomer was installing this saml solution to host platform login, the above url would be https://testcustomer.datagrail.io/saml/metadata
-
Recipient: https://[yourname].datagrail.io/saml/auth
- Example: if TestCustomer was installing this saml solution to host platform login, the above url would be https://testcustomer.datagrail.io/saml/auth
-
ACS Consumer URL: https://[yourname].datagrail.io/saml/auth
- Example: if DataGrail Demo was installing this saml solution to host platform login, the above url would be https://testcustomer.datagrail.io/saml/auth
-
ACS Consumer URL Validator
- Input the regex expression that matches the value of the Consumer URL from step 3.
- Ex: https://testcustomer.datagrail.io/saml/auth is validated as:
^https:\/\/testcustomer\.datagrail\.io\/saml\/auth$Note: ‘/’ and ‘.’ are escaped characters so you need to put a ‘\’ in front of each one. The '^' and '$' characters indicate the beginning and end of the regular expression.
-
SAML not valid before / not valid on or after: 3 (should be the default)
-
SAML Initiator: Default: OneLogin
-
SAML NamedID Format: email
-
SAML Issuer Type: Specific
-
SAML Signature Element: Response
-
SAML Encryption Method: Default to TRIPLESDES-CBC
-
SAML sessionNotOnOrAfter: Set to 1440 (should be the default)
-
-
Select the Parameters section in the left-hand menu.
-
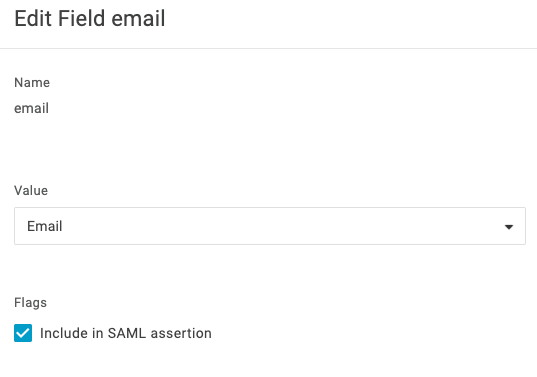
Add a field named email, select Include in SAML assertion, and click save. Once complete, selectEmail from the value dropdown. Click save.
-
Add a field named first_name, select Include in SAML assertion, and click save. Once complete, select First Name from the value dropdown. Click save.
-
Add a field named last_name, select Include in SAML assertion, and click save. Once complete, select Last Name from the value dropdown. Click save.
-
Add a field named is_dg_admin, select Include in SAML assertion, and click save. Once complete, select DataGrail Adminfrom the value dropdown. Click save.
-
Open the SSO section of the left-hand menu. Set SAML Signature Algorithm to SHA-256.
-
Copy the Issuer URL (metadata URL) and send it to: support@datagrail.io
Step 2: Invite Users:
Learn about inviting new users with OneLogin here.
Disclaimer: The information contained in this message does not constitute as legal advice. We would advise seeking professional counsel before acting on or interpreting any material.